Entering the cyber world today is like stepping into a warzone. Cyber is no longer just about isolated hacks or data theft—it has become a persistent battlefield where criminals, businesses, and nation states are locked in constant conflict.
This conflict is often described broadly as cyberwar, but the reality is far more complex. Traditional war is political and nation-driven, while cybercrime is financially motivated and criminal in nature. Both exist in cyberspace, and both are increasing—but the political, nation‑state threat is accelerating much faster.
Defining Cyberwar vs Cyberwarfare
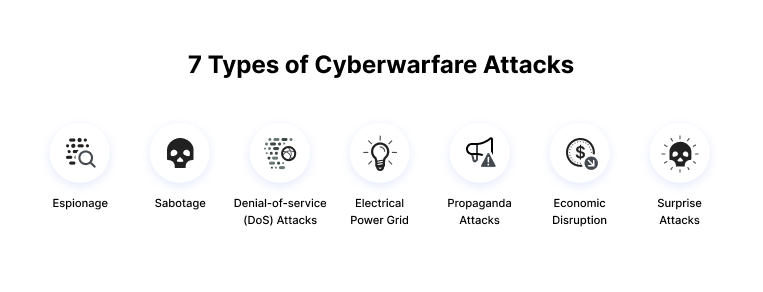
Cyberwar is difficult to define, and experts often disagree on whether a meaningful distinction exists between criminal attacks and nation‑state aggression. From a defender’s perspective, any attack can feel the same.
For clarity, this article makes a deliberate and simplified distinction:
- Cyberwar refers to conflict between criminals and businesses, driven primarily by financial gain.
- Cyberwarfare refers to conflict between nations or ideologically motivated groups, driven by political objectives.
This distinction is not widely adopted, but it helps explain why nation‑state cyber activity poses a fundamentally greater risk. Criminal cyberwar can cripple companies; cyberwarfare can destabilize entire countries.
Motivation Matters More Than Damage
The difference between cyberwar and cyberwarfare is not defined by the scale of damage, but by intent.
- Criminal actors seek fast returns and visible impact—ransom, extortion, or data resale.
- Nation‑state actors play the long game, embedding themselves quietly inside systems for months or years to prepare for future conflict.
Although international norms often define cyberwar acts by physical harm or loss of life, this standard is increasingly inadequate. Financially motivated attacks can also cause real‑world harm, making motivation the most reliable indicator of intent.

Why the Distinction Is Blurring
Many experts argue that defenders no longer need to differentiate between criminal and nation‑state attackers. In practice, tools, tactics, and infrastructure often overlap.
Ransomware gangs may operate with state approval. Nation states may outsource operations to criminal groups. This creates a hybrid threat model where motivations can shift mid‑attack, making prediction and response far more difficult.
As a result, attribution becomes slow, uncertain, and often dependent on classified intelligence that private organizations simply do not have access to.
The Role of International Law and Its Limits
Frameworks like the Tallinn Manual attempt to define what constitutes legal and illegal behavior in cyberspace, particularly for state actors. However, enforcement is weak, and many nations choose to ignore these norms when it suits their strategic interests.
Cyber espionage, including long‑term intelligence gathering, remains largely tolerated under international law—further muddying the distinction between preparation and aggression.
Pre‑Positioning: Preparing the Cyber Battlefield
Nation‑state cyberwarfare is increasingly about pre‑positioning—embedding access inside critical infrastructure long before conflict begins.
This strategy was clearly demonstrated ahead of Russia’s 2022 invasion of Ukraine. Similar tactics are now believed to be underway globally, targeting:
- Energy grids
- Telecommunications
- Transportation systems
- Semiconductor supply chains
- Government and defense networks
By 2026, the consequences of a decade of pre‑positioning may become visible, with cyber battlefields already built deep inside global infrastructure.
The Impact of AI on Cyber Conflict
Artificial intelligence is dramatically reshaping cyberwarfare.
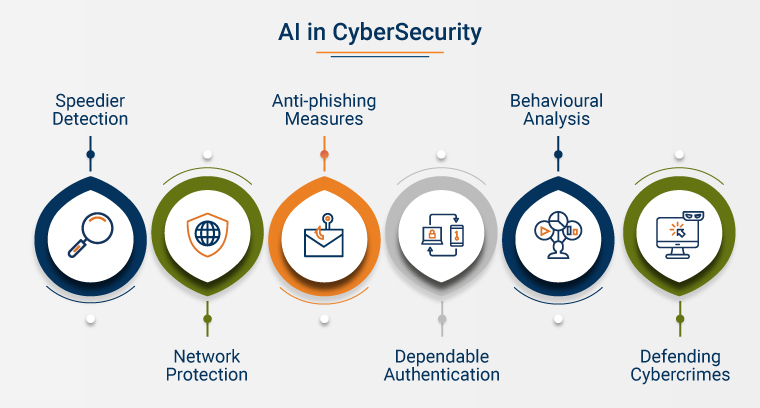
AI lowers the barrier to entry, allowing smaller nations and non‑state actors to conduct highly sophisticated attacks with limited resources. Autonomous AI agents can blend cyberattacks with disinformation campaigns and real‑world disruption at unprecedented scale.
This means future conflicts may begin not with missiles, but with synchronized failures across power, transport, communications, and public trust.
Attribution, Deniability, and Strategic Confusion
Attribution in cyberspace is slow, complex, and politically sensitive. Nation states exploit this by operating through proxies, criminal gangs, or patriotic hackers—maintaining plausible deniability.
Attacks like the Colonial Pipeline incident illustrate this challenge. While the impact was severe, the use of a known ransomware group allowed state actors to deny involvement and avoid escalation.
Attribution has therefore become not just a technical process, but a diplomatic tool.
The Risk of Escalation
Governments are cautious in publicly attributing cyberwarfare because acknowledgment demands response. Any response must be:
- Fully attributed
- Proportionate
- Strategically calculated
A misstep could trigger retaliation, escalation, and potentially kinetic conflict. For nuclear‑armed powers, this risk is existential.
This is why private‑sector “hack‑back” is universally discouraged—one mistake could spiral into international crisis.
Cyberwarfare and Kinetic Response
Major powers have made it clear that severe cyberwarfare—particularly attacks causing loss of life—could justify kinetic military response.
Recent developments, including the UK’s restructuring of its Cyber and Specialist Operations Command and expanded offensive cyber capabilities in both the US and UK, demonstrate that cyber is now fully integrated into military doctrine.
Cyberwarfare is no longer separate from physical war—it is its opening act.
Living in a Cyber Cold War

What we are experiencing today resembles a Cyber Cold War—continuous, undeclared, and constrained by fear of escalation.
Adversaries probe, infiltrate, and destabilize without crossing clear red lines. The hope is that deterrence holds, just as it did during the original Cold War.
Yet unlike the past, digital dependence means the stakes are higher, and civilian infrastructure is deeply exposed.
Final Thoughts: Cyberwarfare is no longer theoretical—it is persistent, global, and growing. As geopolitics worsen, cyber conflict will intensify. Governments, enterprises, and critical infrastructure operators all play a role in resilience. The more secure systems are, the less leverage adversarial states gain.
The fight against cyberwarfare is collective. Stronger cooperation between public and private sectors is not optional—it is essential to prevent the cyber battlefield from turning into a physical one.
#Cyberwar2026 #Cybersecurity #Carrerbook #Anslation #NationStateThreats #Cyberwarfare #DigitalSecurity #CyberDefense
Read More –
- Powerful Man Utd vs. Crystal Palace: Preview, Predictions and LineupsThe battle for Champions League qualification intensifies as Manchester United host Crystal Palace at Old Trafford in a high-stakes Premier League clash. With momentum firmly on their side, United are pushing hard for a top-five finish, while Palace arrive hoping to upset the odds once again in Manchester. Match Preview Carrick’s United Hitting Top Gear… Read more: Powerful Man Utd vs. Crystal Palace: Preview, Predictions and Lineups
- Powerful NASA Crew-11 Emergency: The Historic Medical Evacuation from ISSIn a rare and historic decision, NASA announced the early return of four astronauts from the International Space Station (ISS) following a medical issue involving veteran astronaut Mike Fincke. The unexpected development marked the first-ever medical evacuation from the ISS, drawing global attention to astronaut health and emergency preparedness in space. What Happened in Space?… Read more: Powerful NASA Crew-11 Emergency: The Historic Medical Evacuation from ISS
- Powerful The NASA’s Curiosity Rover Sees Martian ‘Spiderwebs’ Up CloseA hilly landscape that looks like spiderwebs when viewed from orbit is offering new clues about the history of water on ancient Mars. For nearly six months, NASA’s rover Curiosity has been exploring a region filled with unusual geologic formations known as boxwork. These low ridges, standing 3 to 6 feet (1 to 2 meters)… Read more: Powerful The NASA’s Curiosity Rover Sees Martian ‘Spiderwebs’ Up Close
